 At Boxaid online PC repair service we definitely see every kind of computer problem and virus out there on a daily basis. Many are repetitive but some are unique. We thought we would share one virus that did a pretty good job of making the PC very difficult to clean. The malware falls under the generic trojan category which infects a machine by the typical trickery that says “Your PC is infected, click here to remove” when you go to an unsuspecting website. As the user is tricked into clicking the link and downloading the executable to their machine it does the usual stuff of embedding itself in the Windows folder and making sure it starts up when your machine boots up by hiding itself in the registry. None of this is anything new. A subsequent scan with Malwarebytes removes the trojan but Malwarebytes has trouble changing the host file back to its original state. But unfortunately the hosts file has been altered and permissions changed so that you cyou are unable to edit the hosts file back to its original state.
At Boxaid online PC repair service we definitely see every kind of computer problem and virus out there on a daily basis. Many are repetitive but some are unique. We thought we would share one virus that did a pretty good job of making the PC very difficult to clean. The malware falls under the generic trojan category which infects a machine by the typical trickery that says “Your PC is infected, click here to remove” when you go to an unsuspecting website. As the user is tricked into clicking the link and downloading the executable to their machine it does the usual stuff of embedding itself in the Windows folder and making sure it starts up when your machine boots up by hiding itself in the registry. None of this is anything new. A subsequent scan with Malwarebytes removes the trojan but Malwarebytes has trouble changing the host file back to its original state. But unfortunately the hosts file has been altered and permissions changed so that you cyou are unable to edit the hosts file back to its original state.
The Purpose of the Windows Hosts File
The hosts file is part of your Windows operating system and acts like an address book. When you type an address like www.yahoo.com into your browser, the Hosts file is consulted to see if you have the IP address, or “telephone number,” for that site. If you do, then your computer will “call it” and the site will open. If not, your computer will ask your ISP’s (internet service provider) computer for the phone number before it can “call” that site. Most of the time, you do not have addresses in your “address book,” because you have not put any in there. Therefore, most of the time your computer asks for the IP address from your ISP to find sites. This trojan put hundreds of entries in the hosts file to make sure when you type in yahoo.com into your browser you are redirected to one of their fake websites. Of course when you get to their fake website they want you click on one of their links so they can make a few cents on your clicks. That is how they make money.The Hacked Hosts File
Normally, to fix your hosts file (located in c:windowssystem32driversetc folder) you can simply open it in notepad and delete all the entries that the trojan left behind then save the file. Optionally, if you are using a good antivirus program it will take care of that for you. In this case Malwarebytes was unable to fix the hosts file. So we said no big deal, we will simply fix it manually. Take a look at this hacked hosts file that shows all the fake entries in the hosts file. This tells your computer if you try to go to any of the sites listed in the hosts file that you should be redirected to the malware writer’s fake website.
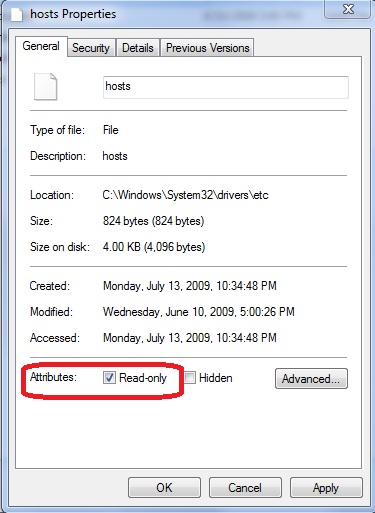
 So we opened up the hosts file deleted all the fake entries and attempted to save and close the file. Windows refused to save the file. So we remembered that many times the hosts file can be marked read only by the malware or even by Windows and we just need to uncheck the read only box in properties of the files.
So we opened up the hosts file deleted all the fake entries and attempted to save and close the file. Windows refused to save the file. So we remembered that many times the hosts file can be marked read only by the malware or even by Windows and we just need to uncheck the read only box in properties of the files.
Windows Permissions Altered on the Hosts File
Well in this case even though we unchecked read-only and hit apply, Windows would not let us save the changes. So we tried to simply delete the file and recreate a new one and still Windows would not let us delete or change the file in any way. This was very odd. We have seen many locked files before left by a virus but typically we are at least able to delete them. So we tried an automated tool called Killbox (this tool is no longer available) that can force the delete of a locked file and this tool didn’t work either. So finally we took a look at permissions of the file and found that the NTFS security permissions were significantly altered. They were restricted enough to the point where we could not change them in the normal properties of the file as shown below.
 As you can see the only group that has permissions to the file is Authenticated Users which means you are unable to edit windows hosts file and can not delete or alter the file in any way including its permissions. Even under advanced settings the Administrators group was removed from the Owners list making it near impossible to change. Finally, after a bit of research we were able to find how to add the permissions back to the file so we could delete it. The goal was to get the administrators group back as the owner of the file so we could just delete the file and create a new empty one. We used the built in Windows command called CACLS which allows you change file permissions in a very granular fashion. There are countless commands and switches to CACLS but here are the key ones that helped us. These commands need to be run from an elevated command prompt. This means when you open the command prompt, you must run it as Administrator as shown below.
As you can see the only group that has permissions to the file is Authenticated Users which means you are unable to edit windows hosts file and can not delete or alter the file in any way including its permissions. Even under advanced settings the Administrators group was removed from the Owners list making it near impossible to change. Finally, after a bit of research we were able to find how to add the permissions back to the file so we could delete it. The goal was to get the administrators group back as the owner of the file so we could just delete the file and create a new empty one. We used the built in Windows command called CACLS which allows you change file permissions in a very granular fashion. There are countless commands and switches to CACLS but here are the key ones that helped us. These commands need to be run from an elevated command prompt. This means when you open the command prompt, you must run it as Administrator as shown below.
 > cacls C:\WINDOWS\system32\drivers\etc\hosts /E /G Administrators:F
> cacls C:\WINDOWS\system32\drivers\etc\hosts /E /G “Your User Name”:F
> cacls C:\WINDOWS\system32\drivers\etc\hosts /E /G Administrators:F
> cacls C:\WINDOWS\system32\drivers\etc\hosts /E /G “Your User Name”:F
We used the first command which worked well and added the Administrators group to the file. At that point all we had to was delete the file and replace it with a new clean hosts file. The clean hosts file typically has nothing in it except one entry and the rest are just comments explaining how the hosts file works. You can find the original hosts file on the Microsoft website here. Well that’s all there is to it. Many viruses will take advantage of the hosts file to do website redirection and normally, after you remove the virus its pretty easy to edit your hosts file but in some cases the malware author will make it as hard as possible to get your machine back to normal.
